In my previous post, I’ve shown how to use DSC to configure the local security policy. If you only want to get the compliance status of the system, Pester might be more suitable.
I first create a hastable of settings like this:
# secedit.exe /export /Cfg C:\secpol.txt /areas SECURITYPOLICY
(Get-Content -Path 'C:\secpol.txt' -ReadCount 1) `
-match '^([A-Z\s0-9_\\]+)=(.*)$' -replace '=',',' |
ConvertFrom-Csv -Header Key,Value1,Value2 | ForEach-Object {
' @{'
" Key = '{0}'" -f $_.Key
" Value1 = '{0}'" -f $_.Value1
if ($_.Value2) {
" Value2 = '{0}'" -f $_.Value2
}
' },'
}
and I populate the file secpol.ps1 using the output of the above command.
The content looks like this. The hashtable is stored inside an array named $SecurityPolicy.


Now in the test file secpol.tests.ps1, I’ve:
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| $here = Split-Path -Parent $MyInvocation.MyCommand.Path | |
| $sut = (Split-Path -Leaf $MyInvocation.MyCommand.Path) -replace '\.Tests\.', '.' | |
| . "$here\$sut" | |
| #region Security policy | |
| Describe 'Security Policy' { | |
| BeforeAll { | |
| & (gcm secedit.exe) @('/export','/Cfg','C:\Windows\temp\secpol.SECURITYPOLICY.txt','/areas','SECURITYPOLICY') | |
| $CurrentSecPolicy = (Get-Content -Path 'C:\Windows\temp\secpol.SECURITYPOLICY.txt' -ReadCount 1) ` | |
| -match '^([A-Z\s0-9_\\]+)=(.*)$' -replace '=',',' | | |
| ConvertFrom-Csv -Header Key,Value1,Value2 | |
| } | |
| $SecurityPolicy | ForEach-Object -Process { | |
| $k = $v1 = $v2 = $null | |
| $k = $_.Key | |
| $v1= $_.Value1 | |
| $v2 = $_.Value2 | |
| if ($v2) { | |
| It "should have its $k policy type set to $v1" { | |
| ($CurrentSecPolicy | Where { $_.Key -eq $k }).'Value1' -eq $v1 | Should be $true | |
| } | |
| It "should have its $k policy value set to $v2" { | |
| ($CurrentSecPolicy | Where { $_.Key -eq $k }).'Value2' -eq $v2 | Should be $true | |
| } | |
| } else { | |
| It "should have its $k policy set to $v1" { | |
| ($CurrentSecPolicy | Where { $_.Key -eq $k }).'Value1' -eq $v1 | Should be $true | |
| } | |
| } | |
| } | |
| } | |
| #endregion |
Let’s see how to use it
Invoke-Pester ~/documents/pester/secpol

Fine, my system is compliant.
But, let’s I change the Maximum password age using gpedit.msc

Now, Pester reports my system as not being compliant:
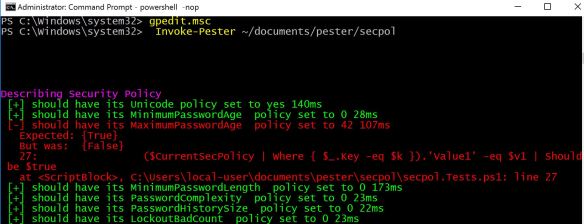
But, the only drawback with my quick’n dirty code is that it doesn’t tell you what value was found instead of the expected 42 in this case.