I’ve been working with many certificates (their private key) used to decrypt back the protected eventlogs (encrypted initially with their public key).
The good news is, you can add as many private keys as you want, they’ll be all be used along to decrypt protected messages. Microsoft did a pretty good job on the Unprotect-CmsMessage cmdlet.
Lee Holmes originally presented in the PowerShell ♥ the Blue Team post how to post-process the content of protected event log messages using the following command:
Get-WinEvent Microsoft-Windows-PowerShell/Operational | Where-Object Id -eq 4104 | Unprotect-CmsMessage
Get-WinEvent is a very powerful cmdlet but it doesn’t know of protected messages natively.
No problem, here’s the way to extend its ability to recognize and decrypt protected messages 😀
First, I import the private keys into my Personal store like this
if (Test-Path -Path "$($HOME)\privatekey_*.pfx" -PathType Leaf) {
Get-ChildItem -Path "$($HOME)\privatekey_*.pfx" | ForEach-Object {
Import-PfxCertificate -FilePath "$($_.FullName)" -CertStoreLocation Cert:\currentuser\My -Password (ConvertTo-SecureString -AsPlainText '12345678' -Force)
}
}
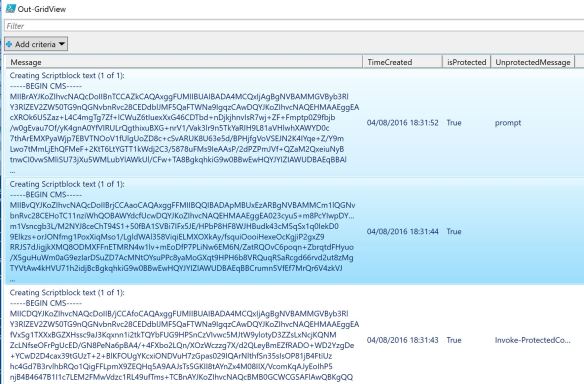
The 2nd step consists in adding the isProtected and UnprotectedMessage properties on the fly and pass it to Out-GridView cmdlet at the end:
| Get-WinEvent -FilterHashtable @{ | |
| LogName = 'Microsoft-Windows-PowerShell/Operational' ; Id = 4104 | |
| } | ForEach-Object { | |
| if (([xml]$_.toXML()).Event.EventData.Data.InnerXml -match '^-----BEGIN CMS-----') { | |
| $_ | | |
| Add-Member -MemberType NoteProperty -Name isProtected -Value $true -PassThru | | |
| Add-Member -MemberType ScriptProperty -Name UnprotectedMessage -Value { | |
| try { | |
| $this.Message | Unprotect-CmsMessage -ErrorAction Stop | |
| } catch { | |
| [string]::Empty | |
| } | |
| } -PassThru | |
| } else { | |
| $_ | | |
| Add-Member -MemberType NoteProperty -Name isProtected -Value $false -PassThru | | |
| Add-Member -MemberType ScriptProperty -Name UnprotectedMessage -Value { | |
| $this.Message | |
| } -PassThru | |
| } | |
| } | | |
| Select Message,TimeCreated,isProtected,UnprotectedMessage | | |
| Out-GridView |
Everything looks normal…

Until,… Notice the second event, it’s encrypted, but I don’t have the private key loaded in my store to decrypt it. Its UnprotectedMessage property is empty.
That doesn’t sound good 😉
Pingback: Dew Drop - August 5, 2016 (#2303) - Morning Dew
Pingback: Encrypt event logs and files with PowerShell and group policies – 4sysops
Pingback: Шифрование журналов событий и файлов с помощью PowerShell и групповых политик - Pagb