You may remember the excellent PowerShell Security series from PowerShell Magazine where I presented a Get-PSAutoRun function to investigate malware persistence ala “Sysinternals autoruns”.
I’ve actually revised its content during the last Christmas holidays and transformed it as a module.
I’ve updated the launch points the original Sysinternals autoruns utility checks and tried to do my best to keep track of what new launch points were added or removed between versions:

You may have noticed that there’s a new category for Office plugins.
I’ve also added some code about the PoweLiks malware although I hadn’t had yet a sample to fully test my detection code:

The code has also undergone a major “quality review” to reduce the number of warnings or issues reported by the PSScriptAnalyzer module.

As you can see, it still complains about using the Get-WmiObject cmdlet and the fact that I sometimes use an empty catch block to avoid returning an error.
What’s next?
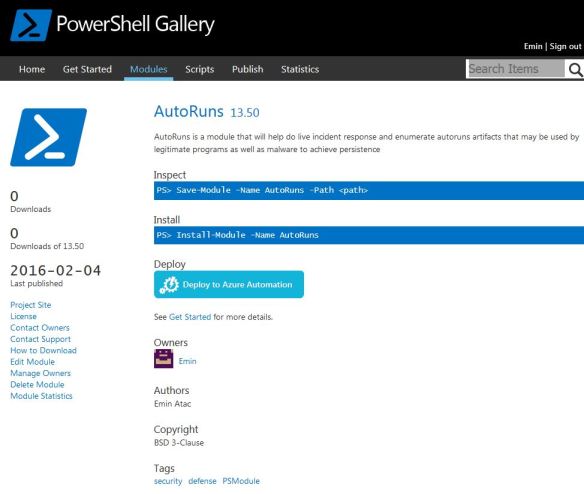
I’ve published the module in the PowerShell Gallery 😀
Now, it’s your turn to test the module and tell me what you think about it. You can also contribute and fork it as it’s stored in my GitHub at this address.
Pingback: First release of AutoRuns module | Tim Bolton - MCITP - MCTS
Reblogged this on Tim Bolton – MCITP – MCTS.